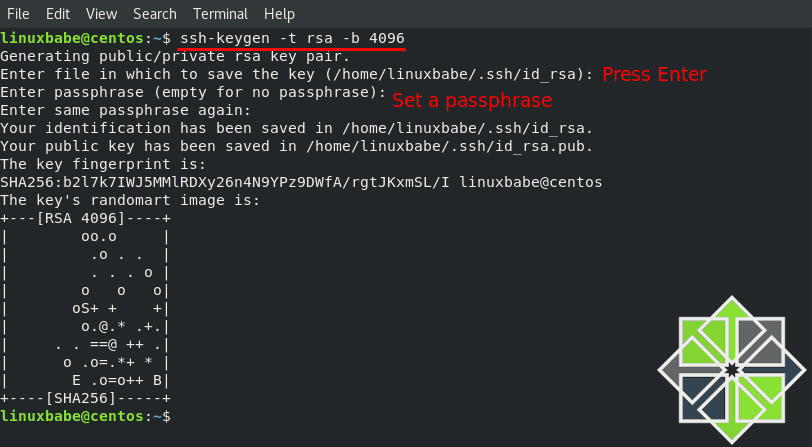
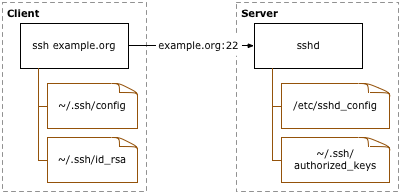
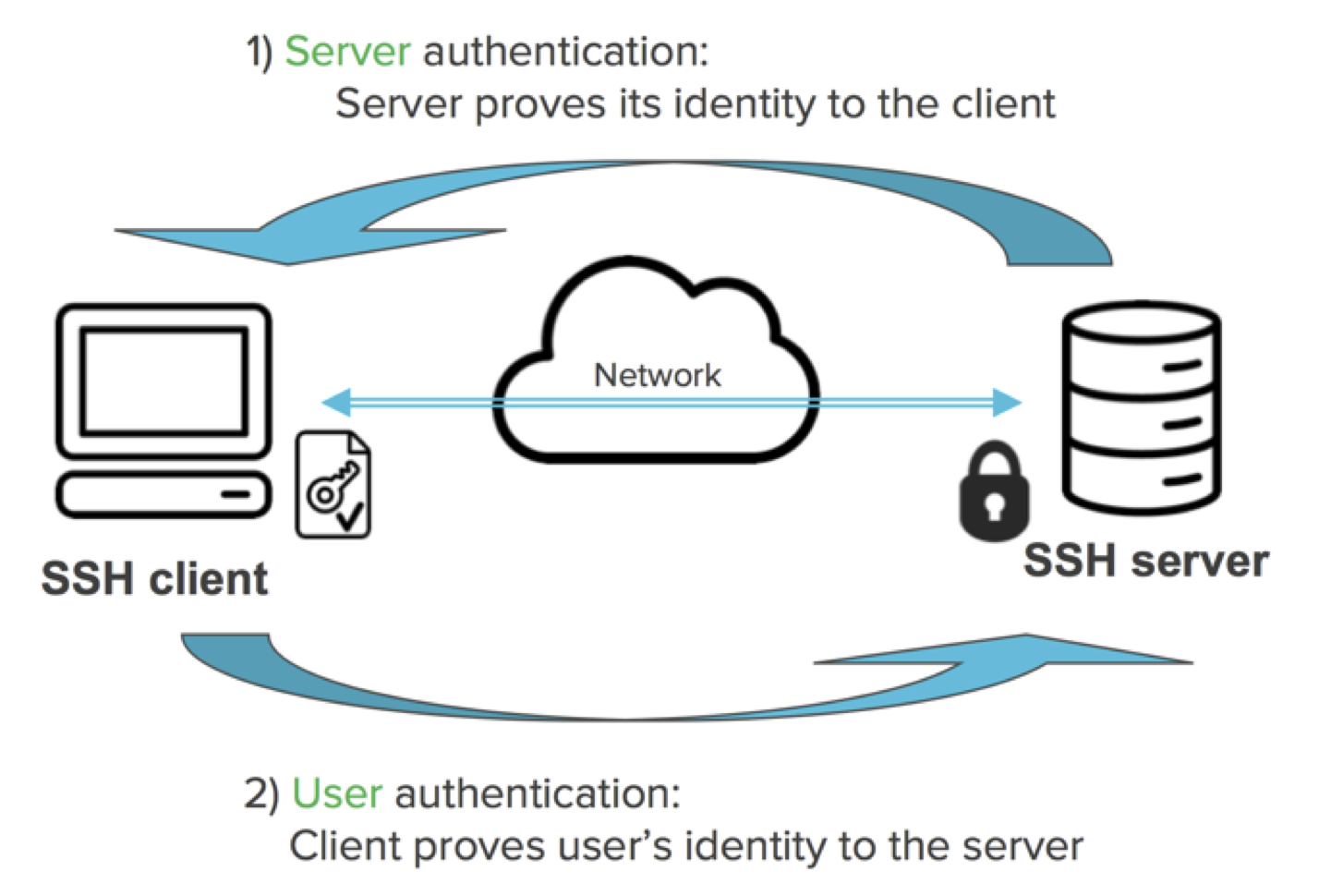
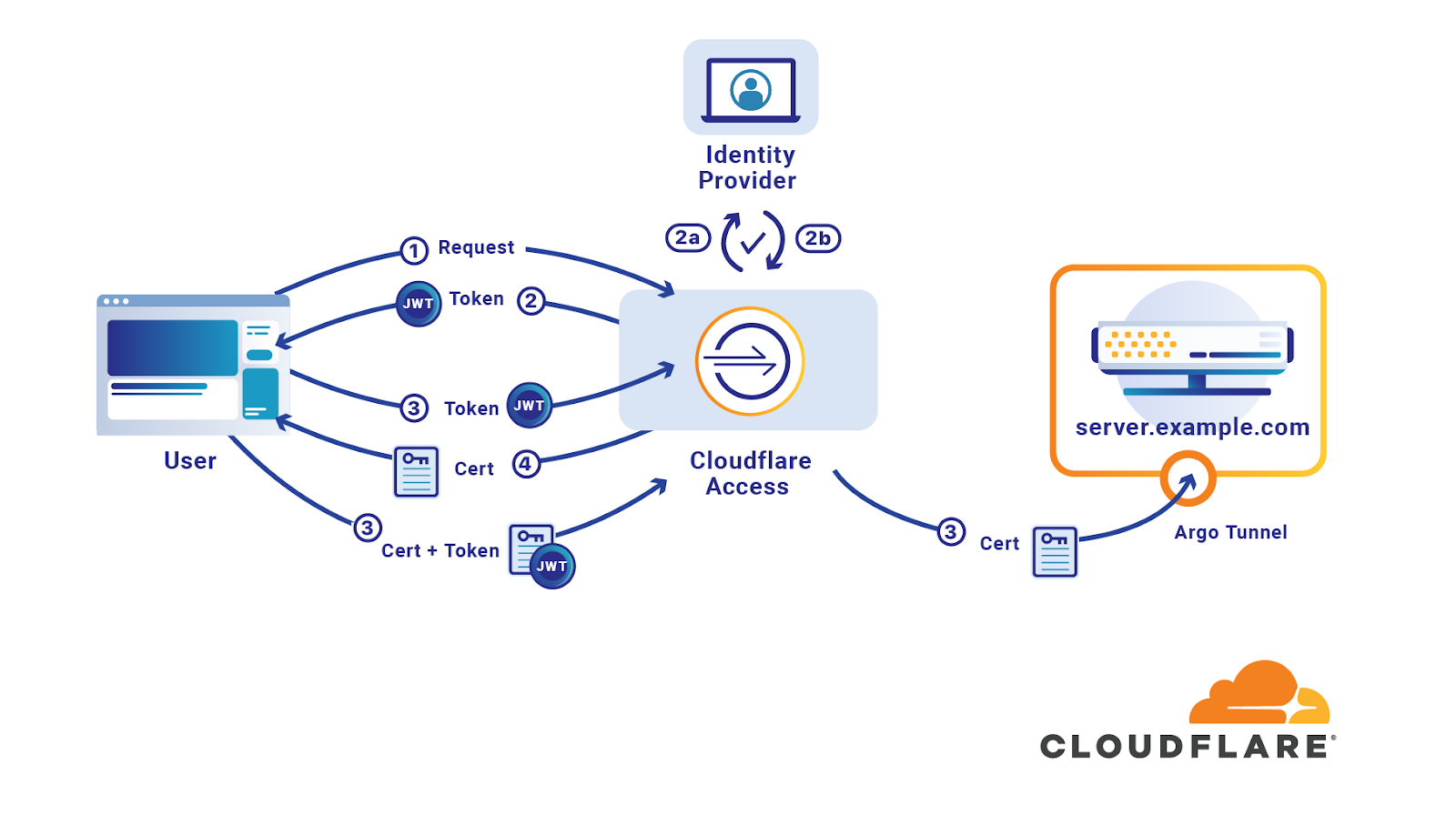
Streamlining Secure Remote Access: A Guide to Passwordless SSH Connections Between Linux Servers | by Prateek Malhotra | Medium
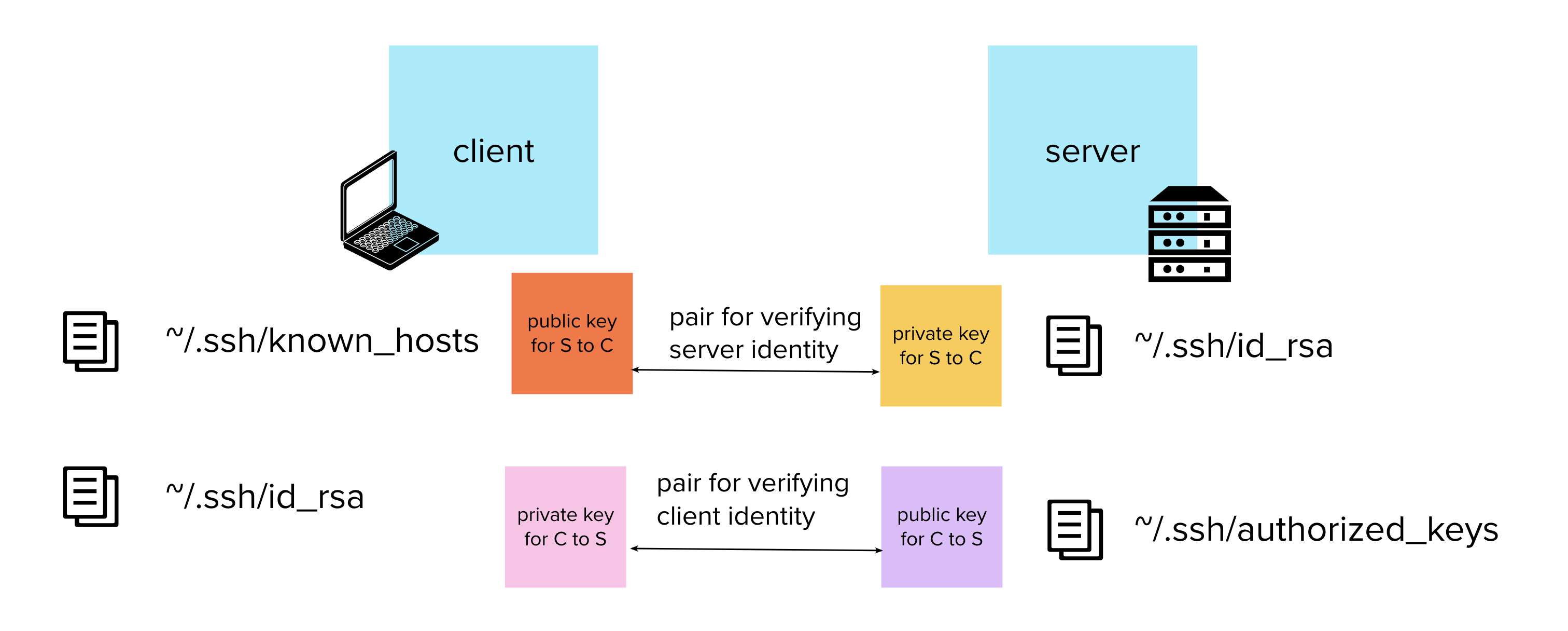
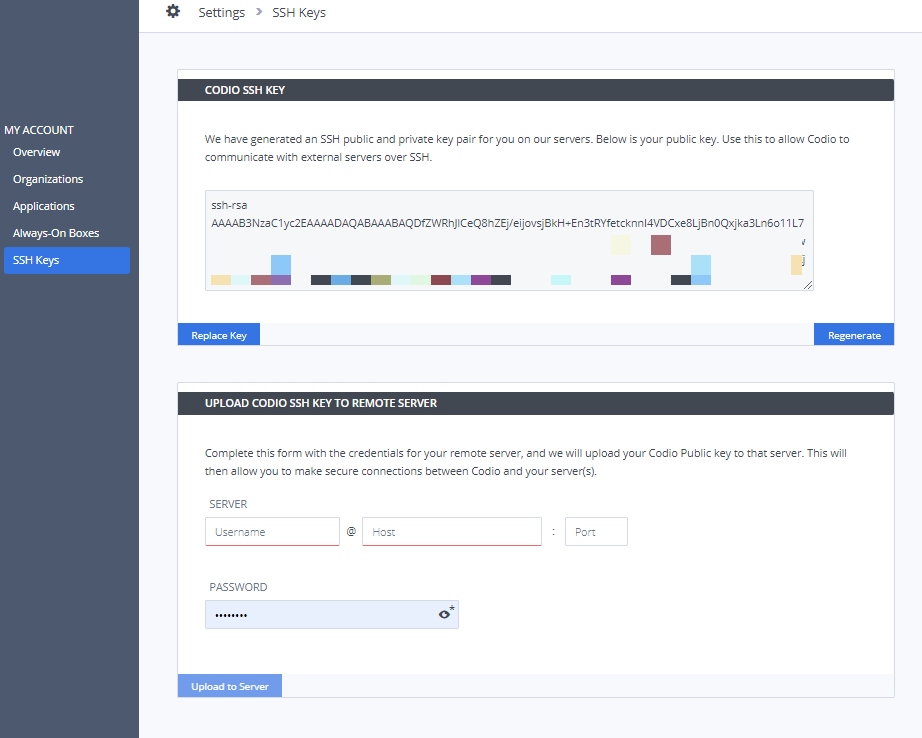
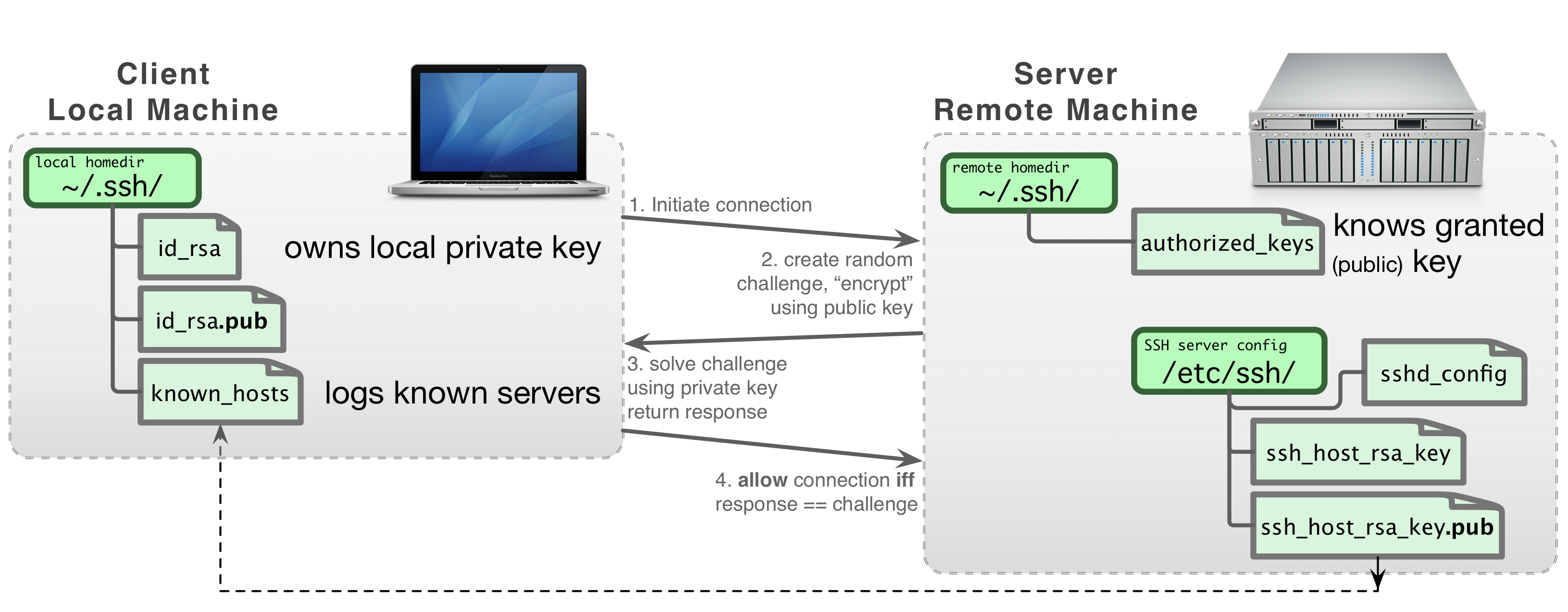
How to properly manage ssh keys for server access :: Päpper's Machine Learning Blog — This blog features state of the art applications in machine learning with a lot of PyTorch samples